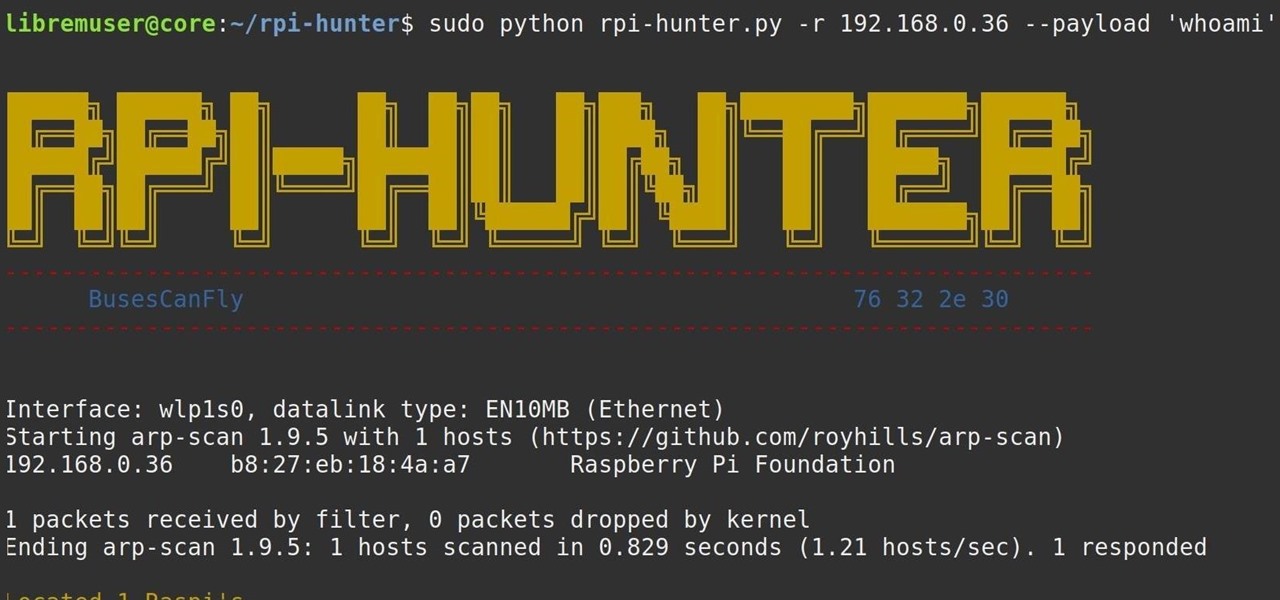
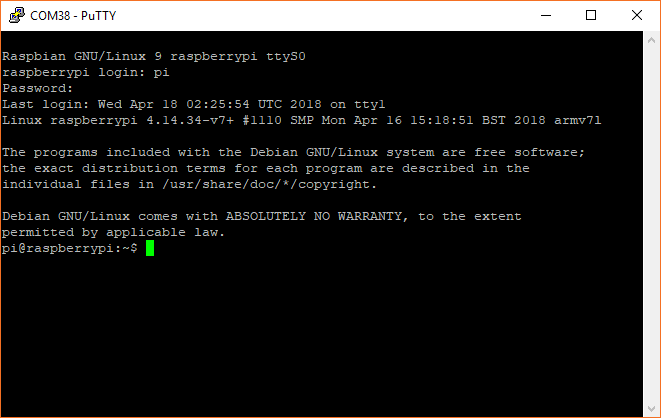
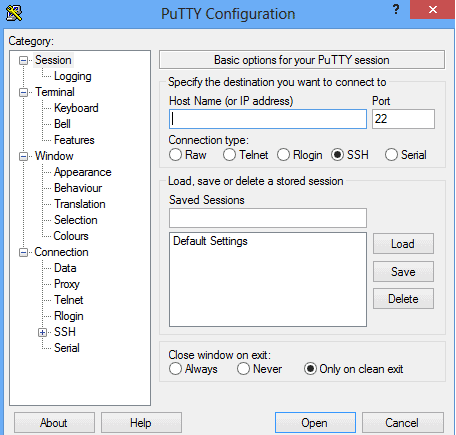
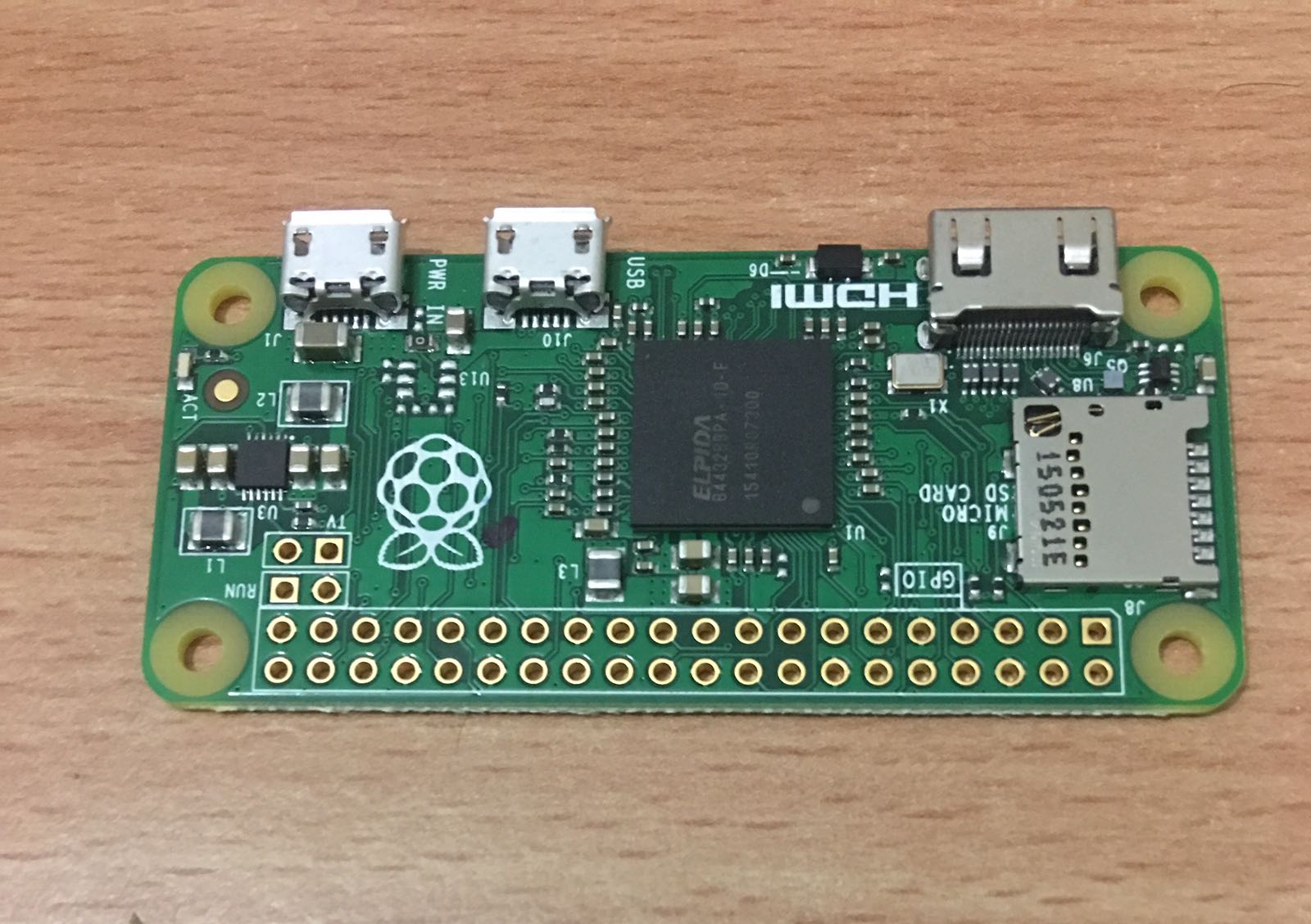
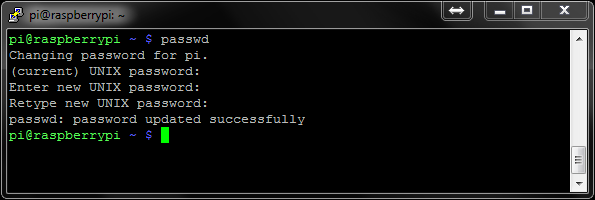
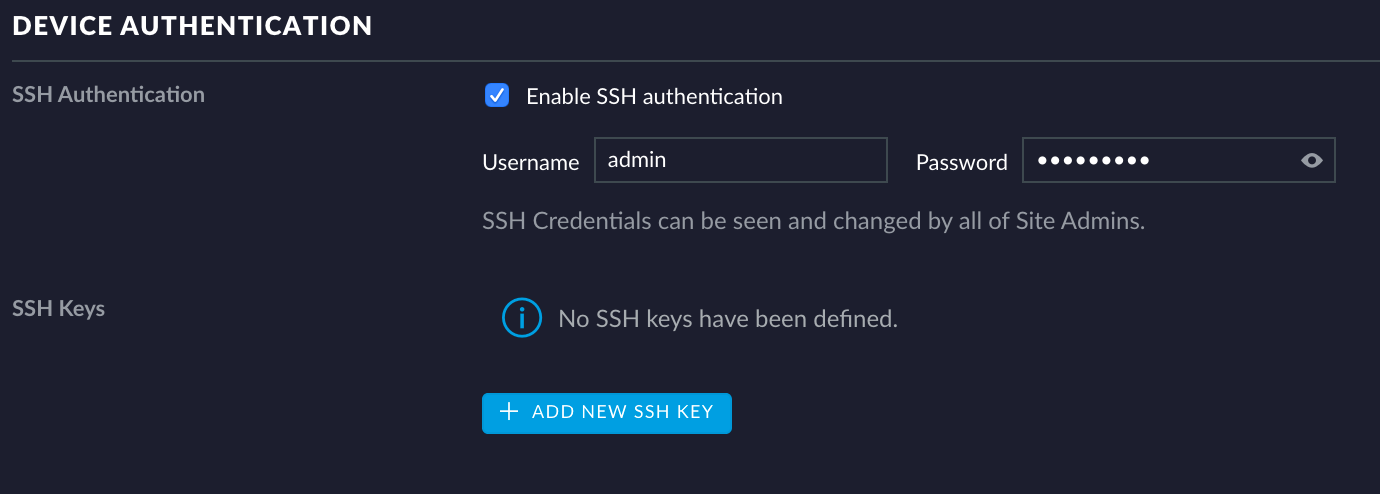
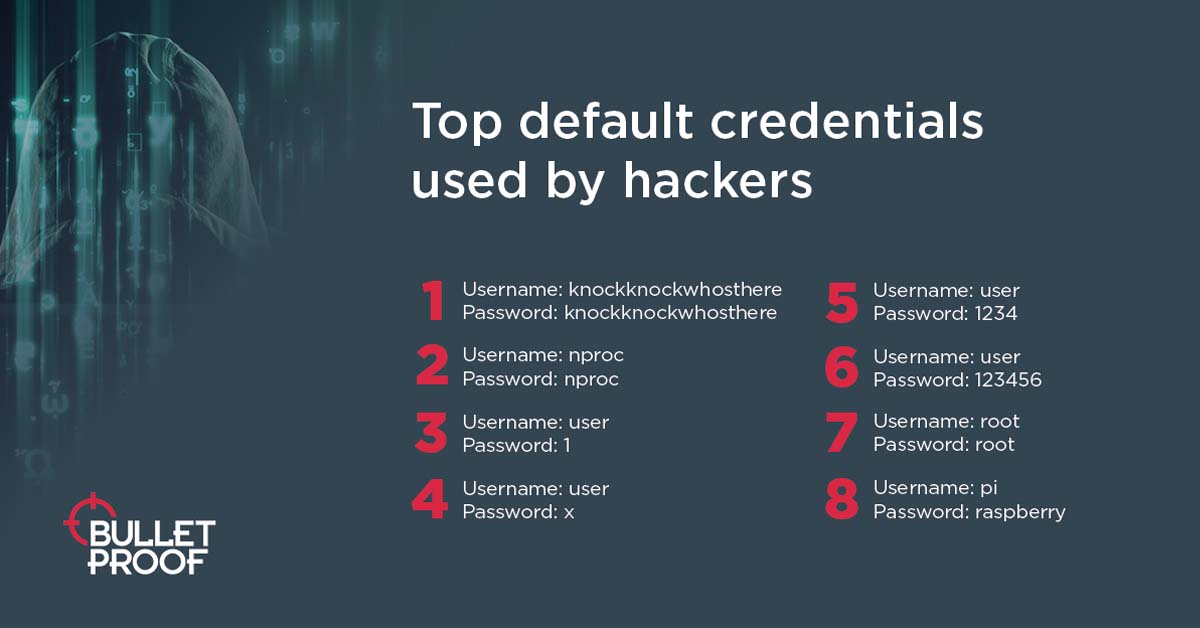
Attackers using default credentials to target businesses, Raspberry Pi and Linux top targets - Help Net Security
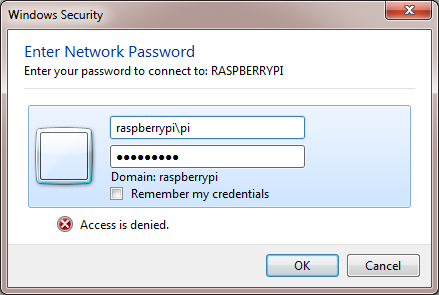
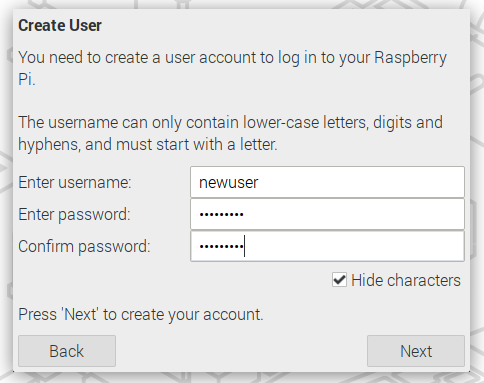
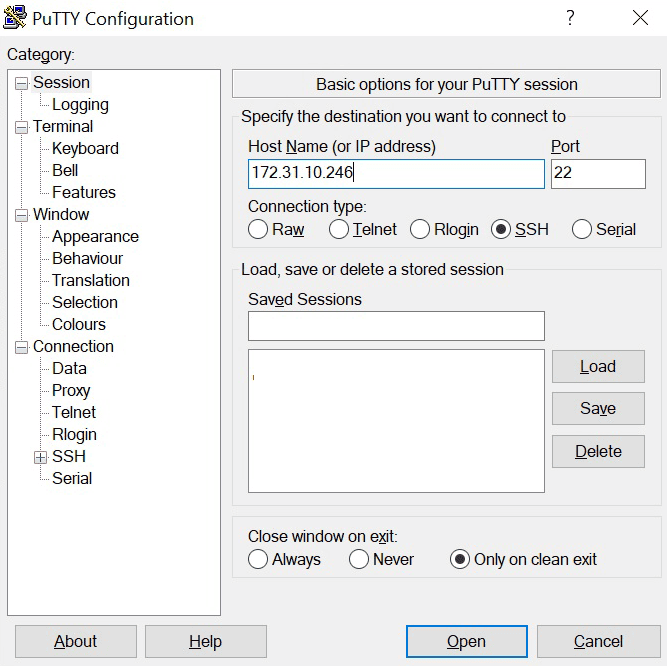
Ubuntu Server Raspberry Pi 4 Image: Cannot login using default credentials "authentication token manipulation error" - The Tech Journal

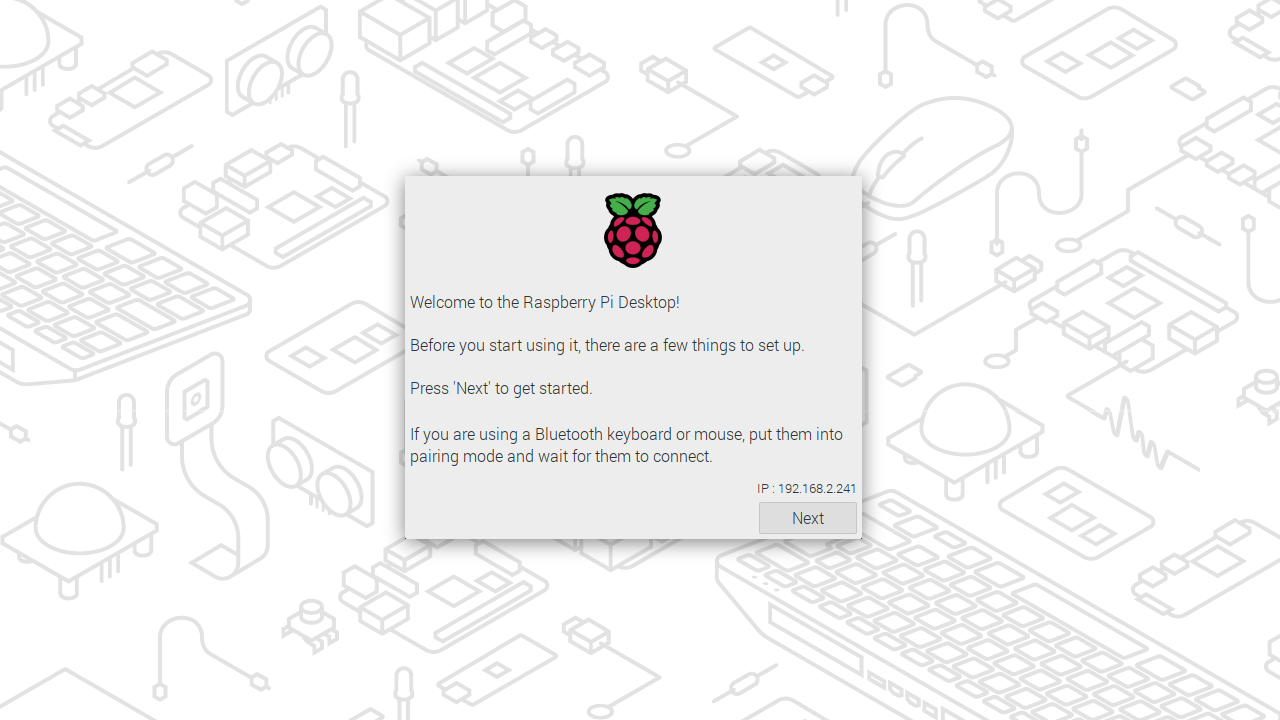
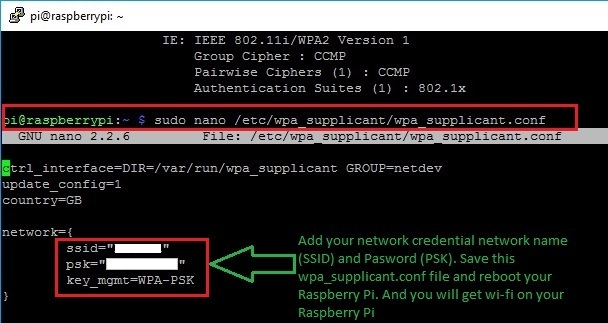
GitHub - schollz/raspberry-pi-turnkey: How to make a Raspberry Pi image that can be deployed anywhere and assigned to a WiFi network without SSH